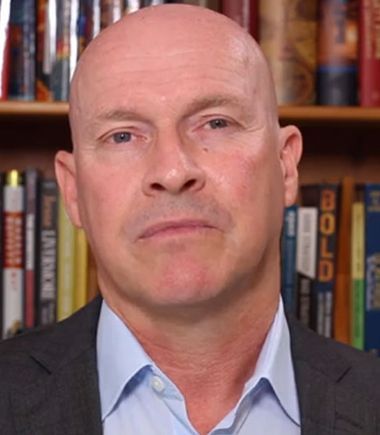
Interview with John Adams, CEO at Waratek

John has a rich history in security and medical technology with his experience spanning more than two decades. Prior to Waratek, John served as president & COO of SecurAmerica, leading the company’s expansion into nearly three-dozen new geographic markets and growing the company from 5 employees to over 5,000. In his career, John has also served as SVP N. America for London-based G4S (formerly Securicor) and held senior executive positions at US Surgical Corporation and Medline Industries. John holds an MBA in Health Care Administration from Webster University and a BS in Business Administration/Accounting from Florida Southern College
TDE: Tell us about your product/business and your specific role?
John Adams: Waratek is a pioneer in the next generation of application security solutions, with a number of fortune 50 companies using Waratek to patch, secure and upgrade their mission critical applications. Using patented technology, Waratek makes it easy for security teams to instantly patch vulnerabilities with no downtime, protect their applications from known and Zero Day attacks, and virtually upgrade out-of-support Java applications – all without time consuming and expensive source code changes or unacceptable performance overhead.
TDE: What is the core issue your product/technology aims to address and what sets it apart from the other players in the market?
John Adams: Waratek is an award-winning pioneer in the next generation of application security solutions. Using patented runtime protection technology, Waratek makes it easy for teams to protect the #1 target for cyber attacks – web applications and servers. Our agents sit on the Waratek ARMR platform and:
- Instantly patching known software flaws with Virtual Patches
- Protecting applications from known and unknown attacks such as the OWASP Top Ten and SANS Top 25
- Virtually upgrading out-of-support Java applications to the most current platform version without rewriting the app
What sets us apart is the use of the JIT compiler for security execution. By leveraging the compiler, we’re able to get closer to the application and provide actual application fixes. Typically, these types of vulnerability fixes would need to be sent back to the development team, which is expensive and time consuming and often means that developers have to sacrifice time that could be spent on product innovation.
TDE: What’s the one industry, sector or role that your technology is most relevant to?
John Adams: Cyber security
TDE: What are some of the common challenges your customers approach you with?
John Adams: Legacy upgrades for out of support applications. For instance, if a customer is using a Weblogic or Websphere server, they are no longer getting support as of December. They are really looking at 2 options – a lengthy, painful re-write or re-platform or an expensive custom support package. Waratek can virtualize the entire JVM, instantly upgrading these servers and allowing customers to continue patching and safeguarding these enterprise critical applications.
Compliance, whether resulting from the previous use case, poor patch hygiene, or fear of broken apps, companies fall behind with security patches. This is often only discovered when an audit surfaces applications that – in some cases – haven’t been patched in years. For these companies to apply 5+ years of patches is not only a strain on resources, but wildly risky. Apps will break, go completely offline, or experience performance impacts from trying to retroactively apply years of security fixes. PCI, Open Banking (PSD2) in Europe, these are all regulations that mandate controls around applications as a threat vector.
Application Security, 80% of application code is comprised of third-party code and libraries often from open-source contributors. Even the most secure developers can’t predict flaws in code they don’t write.
TDE: Using technology to effect transformation usually starts with a transformation of beliefs and mindsets. How do you consult enterprise clients and help them make that important shift in mindset to move ahead on a particular project or implementation?
John Adams: The security ecosystem believes programmers should manually fix all their vulnerabilities than automating solutions. As a result, it’s the mid-1990’s all over again when memory management bugs surfaced. Now, the runtime/compiler can automatically fix the bugs without making mistakes than the programmer writing bad code. This tipping point for appsec vulnerabilities could not be reached before with network-based appsec solutions (WAFs, NGFWs, RASPS, etc), but now with JIT-compiler-based solutions that fix vulnerabilities and don’t produce false positives It’s this tipping point to reinforce automatic solutions prevail over the manual alternative. Further, companies have spent decades building and customising monolithic applications. In order for these companies to take advantage of digital transformations, like cloud, often they are looking at complete refactoring projects. This is extremely expensive, takes a great deal of time, and frankly – still has a pretty high rate of failure. Leveraging our virtual upgrades, for instance on AWS, allows our customers to take these applications that might be stuck on an old version of Java (see weblogic/websphere), virtually upgrade, and then they can use open JDKs like Corretto to modernise these apps at no cost. Not only are they getting the benefits of cloud, they’re also reducing the cost and reliance on platform companies which have chosen auditing as their monetization strategy, instead of innovation.
TDE: Give us an example of an enterprise meeting a cybersecurity transformation goal through your product?
John Adams: We have a major manufacturer that will be using our technology to upgrade their servers, move to Corretto, and they will actually have “legacy” applications running in Java 11 before a single greenfield application is on Java 11.
TDE: What present or upcoming technologies you think have the maximum potential to accelerate enterprise security transformation?
John Adams: I don’t think a single offering from Waratek will maximise the potential of enterprise transformation, because it’s not an initiative that can be solved by technology alone. In order to transform, especially in the context of digital transformation, it requires people, processes and technology. That said, the Waratek ARMR platform offers a way to modernise infrastructure, secure any application with true code fixes, and – if preferred – offer more traditional perimeter security controls like WAF. Having a comprehensive set of application security technologies allows companies to focus on initiatives like training and skill development, process improvements like DevOps, or simple to innovate products that further the overall business strategy.
TDE: What’s your go to resource – websites, newsletters, any other – that you use to stay in touch with the explosive changes happening in the digital space?
John Adams: I keep very close to our partner communities – AWS in particular is always raising the bar on transformation thought leadership. When it comes to application security, OWASP is a great resource.
TDE: Read a good book lately on digital transformation that you’d like to recommend to us?
John Adams: I don’t read as much as I’d like, but I did pick up Loonshots by Safi Bahcall recently.
For more DX insights follow John Adams on LinkedIn


 By
By