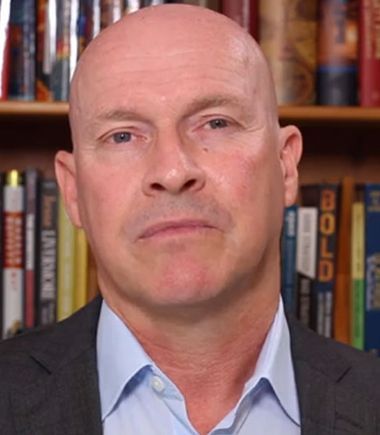
Interview with David Sikora, CEO at ALTR

In this interview, David Sikora, CEO at ALTR elaborates on blockchain’s “digital truth”, why enterprises need to start treating data like they do their money, addressing data breaches in the midst of a digital initiative and stresses the need for a proactive rather than a reactive approach to security. David is a software industry veteran, and has previously served as CEO of 2 public and 5 private, venture capital backed software companies and has held board of director positions with 4 public companies. He is an alumnus of the University of Houston and Harvard Business School
TDE: Tell us about your product/business and your specific role?
David Sikora: I’m the CEO at ALTR, and have been in the tech industry for more than 20 years, including serving as the executive chairman at Stratfor, and leadership roles at Digby, Motive and Pervasive Software.
ALTR has been getting a lot of attention since recently emerging from nearly 4 years of stealth R&D. We have launched the first commercial software package that unlocks the security benefits of blockchain for the enterprise.
It may be useful to give you some context around why we have decided to launch ALTR. As more and more companies are jumping on board with cloud and IoT, new threat vectors to data are continually being introduced –Jupiter Research estimates the cost of these threats will exceed $8 trillion by 2022. It’s a toxic mixture of temptations and economic incentives that reward bad actors, who are always one step ahead of security providers, trapping them in a losing cycle of software patches and new applications.
That’s where ALTR comes in. Our platform is based on proprietary blockchain technology called ALTRchain. This is the first and only high-performance, enterprise-ready blockchain for data security. In fact, we are the first company to commercialize blockchain technology for this purpose and see this as a fundamental shift away from failed perimeter systems.
TDE: What is the core issue your product/technology aims to address and what sets it apart from the other players in the market?
David Sikora: In our view, we have a choice between change or breach. Network-focused security isn’t enough because it can never reduce the sheer number of vulnerabilities. If the current “cyber security industrial complex” were so effective, then we have to ask ourselves “why are there so many breaches?” and “why are they happening with increased frequency?”
I mentioned that we spent 4 years in R&D creating the ALTR platform. It was the need to create a new security architecture that actually led us to blockchain, and not the other way around. Experts have been talking about the cybersecurity potential of blockchain for a long time. Rather than continually trying to put band-aids on the existing attack surface in an enterprise, we have found a way to reduce it to potentially zero using patent-issued blockchain technology. In the purest architectural sense blockchain has the capacity to create “digital truth” – we have harnessed this capability to allow an organization to monitor, govern and protect their critical data in ways that have not been done until now.
TDE: What’s the one industry, sector or role that your technology is most relevant to?
David Sikora: I’ll answer this by focusing on a role. Our technology is the most relevant to the CEO and the Board of Directors at any large enterprise that houses sensitive data – either critical customer data or sensitive digital intellectual property.
The enterprise has to start treating its data like it does its money, meaning that the executive suite builds competency in understanding how it flows and what it means, makes policy for how it is used and accessed, and exerts control in governing and protecting it.
Our approach is to transform the way data is monitored, accessed, and stored, and to do that in such a way that is not only protective of the business, but enables it as well.
We’ve crafted a toolkit that deals with data in a way that stakeholders outside of IT can understand and manage.
TDE: What are some of the common challenges your customers approach you with?
David Sikora: Our customers and partners recognize more and more that network-focused security solutions are not sufficiently addressing data breaches, and this is never felt more painfully than when a customer is in the midst of a digital initiative that opens their network up to a whole new class of vulnerabilities. The most common network disruptors are cloud migrations, mobility initiatives, and system overhauls. It’s at those times that executives on both the business and the IT side are looking at how to protect sensitive data that is suddenly being stored in new places and used in new ways.
We are also leaned on to protect the data in vulnerable legacy applications because of how our smart drivers have no impact to existing application or database function or configuration.
The common thread is that customers need to be able to see all data access activity, slow down or block that activity in real time when it’s inappropriate and protect data at rest without impacting application function. We solve those problems, and dramatically reduce threats to data.
TDE: Using technology to affect transformation usually starts with a transformation of beliefs and mindsets. How do you consult enterprise clients and help them make that important shift in mindset to move ahead on a particular project or implementation?
David Sikora: Spending on cybersecurity is ramping 20% year over year, and yet so are the frequency and severity of data breaches. How did we get here?
It’s because for the first 20 years of this connected computing revolution we focused solely on speed and convenience with very little attention to security in the basic designs of our systems.
Now we find ourselves stuck in a “patch culture” where, like the little boy sticking his finger into leaks in the dam, we react to every new exploit with a patch. Many of the popular cybersecurity products themselves are just giant patches. By the time the solution has become adopted, the bad guys have moved on. Many cybersecurity leaders, many business executives, are waking up to this, and it’s this new mindset that is leading them to consider more transformational, proactive approaches.
What we focus on as a company are fundamentally new ways of thinking about our systems.
Blockchain is a perfect example of a new design pattern for data storage that is secure by design. Making database drivers smart arbiters of data consumption is a fundamental re-tasking of what used to be just a dumb pipe. These innovations are deep in the stack, and their impact is profound.Don’t patch the dam, design a stronger one.
TDE: Give us an example of an enterprise meeting a digital transformation goal through your product?
David Sikora: We like to say that we make the cloud safe for the enterprise. As well-appointed as the security teams and their toolkits are inside the largest cloud hosts, it does not change the fact that physical resources are shared with unknown parties and physical control is given over as companies move to the Cloud.
Our platform changes that. With sensitive data fragmented, scattered into a private, permissioned ALTRchain node network physical access to any single node is meaningless. Nodes can be distributed across multiple cloud providers, or across a single cloud provider and an owned data center. All data access activity into the node network is logged immutably for compliance purposes.
Now the two biggest obstacles to cloud adoption, data security and compliance, are overcome. Digital trust has come to the Cloud, and now the business can derive the transformational business benefits it can bring without the risks.
TDE: What present or upcoming technologies you think have the maximum potential to accelerate enterprise digital transformation?
David Sikora: Clearly the combination of large and growing datasets, especially with the Internet of Things contributing, and machine learning used to interpret those datasets will continue to serve as the next frontier of enterprise performance. We’ll start to see companies that are able to use those technologies derive significant advantages across a number of operational arenas – from assembly lines to multi-channel marketing.
However, unless they are secured, these technologies that continue to focus on speed and intelligence will be brought down by the dramatic growth in the global cybersecurity threat. So really the greatest enabler of digital transformation will be the new technologies, the new system designs, that protect it.
TDE: What’s your go to resource – websites, newsletters, any other – that you use to stay in touch with the explosive changes happening in the digital space?
David Sikora: I’m a news junkie in general and read Wall Street Journal, New York Times, Washington Post on a daily basis. For tech updates, I find CB Insights, Techcrunch, Business Insider and of course The Digital Enterprise to be solid “go-to” resources. I am also curious about geopolitical trends and country analysis as I find them to be predictive about longer term risks and opportunities in business and government – for this I go to Stratfor, The Economist and a niche publication called The Cipher Brief.
TDE: Read a good book lately on digital transformation that you’d like to recommend to us?
David Sikora: I’ve read quite a few, but in the spirit of being “old school” I would recommend “Business Adventures” by John Brooks. The great thing about the book is it walks you through multiple business and industry transformations that occurred many years ago, proving that change is timeless and patterns can be recognized and hopefully, anticipated. If you’re looking for something more current, then “Hit Refresh” by Microsoft CEO Satya Nadella is an excellent read.
For more DX insights follow David Sikora on LinkedIn and Twitter.


 By
By